Cybersecurity Maturity Model Certification (2.0)
- Home
- Cybersecurity Maturity Model Certification (2.0)

Cybersecurity Maturity Model Certification (2.0)
Information Security is becoming an ever more important component of everyday business.
While organizations may focus on the easy to identify risks, any organization using the internet or has public-facing components are exposed to countless cyber threats at any given moment.
Spam Defense
Simplify your inbox and enhance security with our anti-phishing solution
MFA Setup
Enhance security seamlessly with our quick Multi-Factor Authentication (MFA) guide.
EM+S Security
Essential security features, seamlessly implemented by our experts.
Cybersecurity Maturity Model Certification (2.0)
In 2020 we all faced unexpected delays in business because of a global pandemic, but one area we cannot backslide is cybersecurity. The federal government has already committed and assured contractors that Cybersecurity Maturity Model Certification (CMMC) will continue to be rolled out on schedule and without delay. The first official version of the CMMC was released on January 31, 2020.
On November 4, 2021, the Department of Defense released a revised version of the Cybersecurity Maturity Model Certification and is now commonly referred to as CMMC 2.0.
*****Latest updates*****
On May 10, 2023, NIST released a revised version of NIST 800-171 Revision 3 It is currently in draft phase awaiting comments, but this could potentially mean changes to the CMMC 2.0 standard and the necessary assessment criteria. Giga-Green is closely monitoring changes and actively communicating with our customers regarding potential impacts to their certification enclaves.

What is Cybersecurity Maturity Model Certification (CMMC 2.0)?
This is a necessary evaluation and 3rd party issued certification for Defense Industrial Base (DIB) affiliated businesses that determines by your cybersecurity posture. The federal government has deemed cybersecurity a critical component of contracting, bid award criteria, and will be a requirement for contracting going forward. Giga-Green Technologies has been closely aligned with the NIST 800 series since our inception in 2016 and have been actively working with DoD contractors since 2020 to secure physical and cloud environments to NIST 800-171 standards.
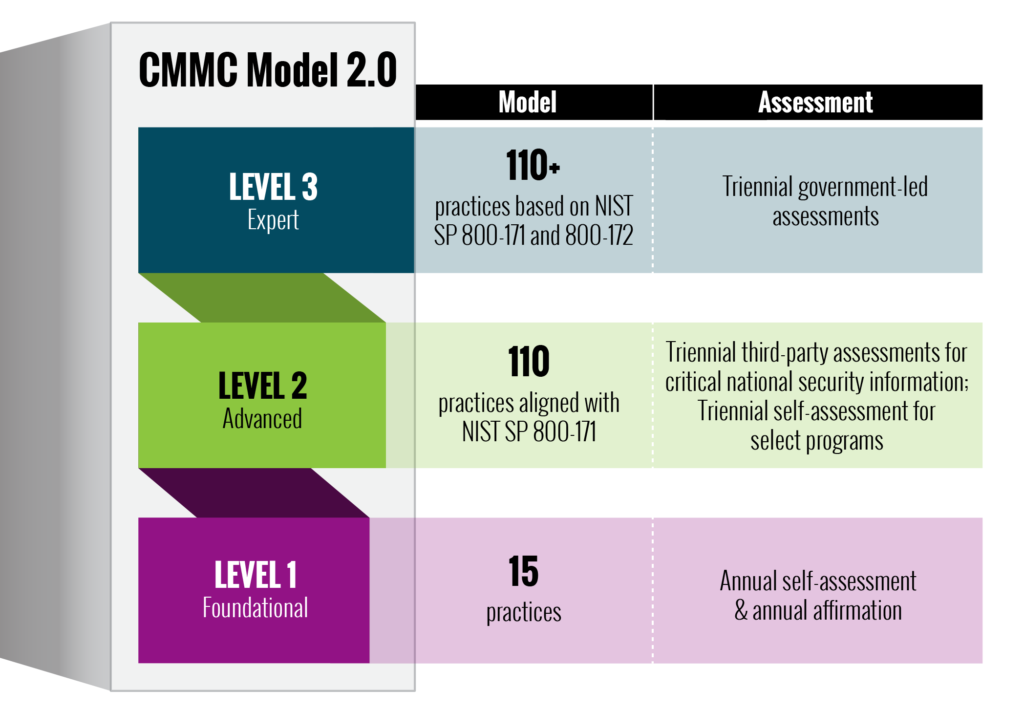
CMMC 2.0 consists of three progressively secure levels of certification built around 17 different domains of cybersecurity and organizational health. We’ve listed the 14 evaluation criteria and brief descriptions below. These knowledge domains were developed from NIST 800-171 standards and have been assigned minimum levels of compliance to achieve a CMMC 2.0 certification. Currently, a CMMC 2.0 certification is anticipated to be valid for 3 years and then be reassessed.
What do these changes entail from the originally proposed CMMC 1.0? The DoD provides the following graphic to align the changes between CMMC 1.0 and CMMC 2.0.
Generally simplified from version 1.0, CMMC 2.0 aims to align more closely with the already enacted FAR (52.204-21) and DFAR (252.204-7012) clauses.
What is Cybersecurity Maturity Model Certification (CMMC 2.0)?
This is a necessary evaluation and 3rd party issued certification for Defense Industrial Base (DIB) affiliated businesses that determines by your cybersecurity posture. The federal government has deemed cybersecurity a critical component of contracting, bid award criteria, and will be a requirement for contracting going forward. Giga-Green Technologies has been closely aligned with the NIST 800 series since our inception in 2016 and have been actively working with DoD contractors since 2020 to secure physical and cloud environments to NIST 800-171 standards.
CMMC 2.0 consists of three progressively secure levels of certification built around 17 different domains of cybersecurity and organizational health. We’ve listed the 14 evaluation criteria and brief descriptions below. These knowledge domains were developed from NIST 800-171 standards and have been assigned minimum levels of compliance to achieve a CMMC 2.0 certification. Currently, a CMMC 2.0 certification is anticipated to be valid for 3 years and then be reassessed.
What do these changes entail from the originally proposed CMMC 1.0? The DoD provides the following graphic to align the changes between CMMC 1.0 and CMMC 2.0.
Generally simplified from version 1.0, CMMC 2.0 aims to align more closely with the already enacted FAR (52.204-21) and DFAR (252.204-7012) clauses.
CMMC 2.0 Level 1 – Federal Contracting Information (FCI) will need to be safeguarded with 15 documented practices and controls
CMMC 2.0 Level 2 – Controlled Unclassified Information (CUI) will need to be safeguarded with 110 documented practices and controls (NIST 800-171)
CMMC 2.0 Level 3 – Under development (NIST 800-172)
How to prepare for a CMMC 2.0 evaluation
The first question we are asked is “Where do we start?” Our process is the same used and recommended by the NIST 800-Series documentation. A high level overview of the required steps and their respective NIST publications are outlined below:
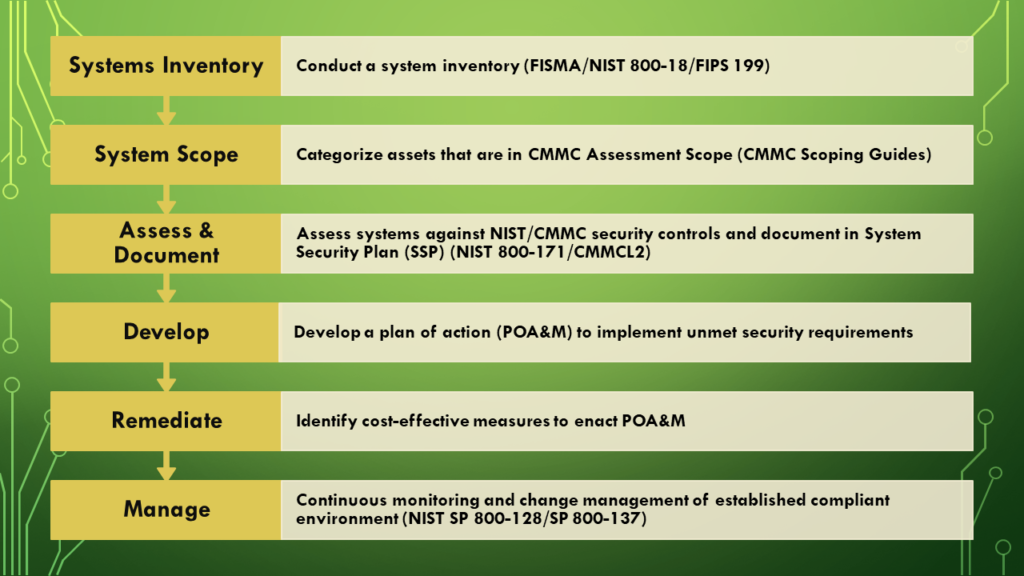
Too much? Many of our customers have and would say this looks daunting… and we are only at the start.
Want to know more about each of these steps and what each include? Take a look at how to identify FCI/CUI, scope and categorize assets, assess your systems, and build documentation by visiting our detailed CMMC preparation page located here:
NIST 800-171/CMMC 2.0 Assessment Domains:
The assessment domains between NIST 800-171 and CMMC 2.0 will remain unchanged and are applied across all in-scope systems. The 14 domains include:
- Access Controls (AC) – Limiting user access to information systems
- Audit & Accountability (AU) – Ability to track user actions to the individual
- Awareness and Training (AT) – Measures taken to educate your workforce
- Configuration Management (CM) – Appropriate configuration, limitation, and use of documented systems
- ID & Authentication – (IA) – Identifying end users correctly and their ability to access systems (multifactor authentication at CMMC 2.0 Level 2)
- Incident Response (IR) – Cybersecurity breach and organizational disaster recovery and business continuity planning
- Maintenance (MA) – Performance of regular maintenance and software updates
- Media Protection (MA) – Proper disposal, transfer, and housing of FCI and CUI data
- Personnel Security (PS) – Screening and authorizing users before accessing data, prevention of data loss through employees
- Physical Protection (PE) – Limiting physical access to resources and monitoring building activity
- Risk Management (RM) – Identifying and mitigating environmental vulnerabilities
- Security Assessment (CA) – Develop, document, and continually improving security postures
- Systems and Communications Protections (SC) – Defining and controlling environment security boundaries, and monitoring for appropriate usage
- System and Information Integrity (SI) – System updates, identifying malicious content, employing monitoring systems to maintain integrity, protecting e-mail communications
CMMC 2.0 Self-Assessments
Words from Our Clients

Moonkle LTD,
Client of Company
SoftTech,
Manager of Company
Moonkle LTD,
Client of Company
SoftTech,
Manager of CompanyTalk to an Expert
Do you have questions or curious about the different solutions and services Giga Green provides?
Our Address:
Tucson/Phoenix, Arizona, USA Minneapolis/St. Paul, Minnesota, USA Fargo, North Dakota, USA
Our Mailbox:
info@giga-green.com
Our Phone:
(701) 630-7188





